Crypto map based with ivrf cust1 vrf and fvrf internet vrf.
Front door vrf ipsec.
The routing instance that is used if no specific vrf is defined.
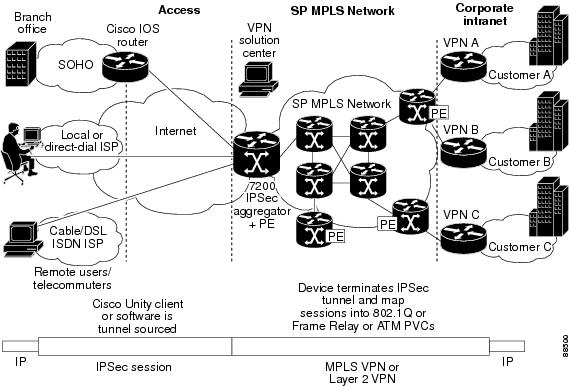
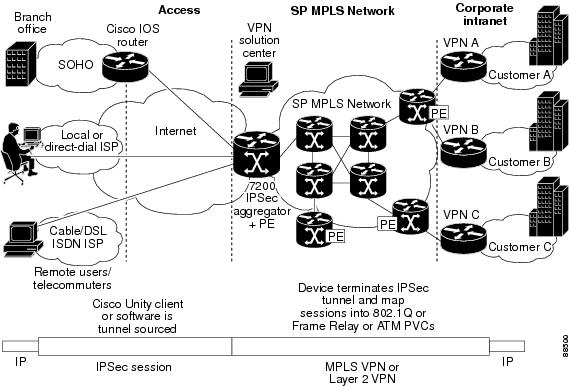
Figure 1 0 shows a typical scenario below this scenario is common amongst service providers and geographic separation is normally sold as part of the solution.
Defining the pre shared key crypto keyring dmvpn vrf dmvpn pre shared key address 0 0 0 0 0 0 0 0 key cisco when you are using a front door vrf you can t define the key using the old crypto isakmp key command.
Front door vrfs in a tunneled environment are really quite cool.
Stated another way the local endpoint of the ipsec tunnel belongs to the fvrf while the source and destination addresses of the inside packet belong to the ivrf.
The outer encapsulated packet belongs to one vrf domain called the front door vrf fvrf while the inner protected ip packet belongs to another domain called the inside vrf ivrf.
Front door vrf or outside vrf the vrf that contain the encrypted traffic.
If no vrf aware config is used everything is done in the global vrf and all interfaces are in the global vrf.
In this post i want to show how to configure dmvpn with ipsec with tunnel source destination ips located in a separate vrf.
Dmvpn and ipsec with front door vrf 24 february 2017 9 min read.
Under the geographic separation scenario eompls would normally be used to link the two ip networks.
Cisco s validated design cvd for iwan suggests the use of front door vrfs in an iwan environment.
The concept is called fvrf ipsec or in english front door vrf ipsec.